
The Real Identity Blog
Socure’s Real Identity Blog is the best source to learn about identity verification and fraud decisioning trends, news, and best practices.
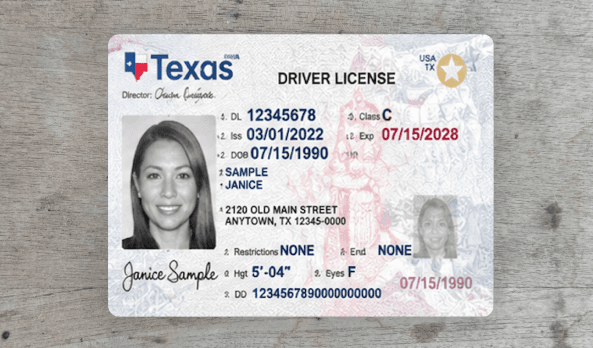
See the Full Story: How Session Recording in DocV Strengthens Fraud Detection and Decisioning
A static signal, like a document or live selfie, might look legitimate. But in today’s fraud landscape, that snapshot is only part of the story. And what you can’t see can cost you.
Modern fraud does not happen in isolated moments.
All topics
Let us prove it.
Join the 3,000+ top enterprises that trust Socure. Speak with one of our identity verification and fraud experts today.